Threat Intelligence Quality
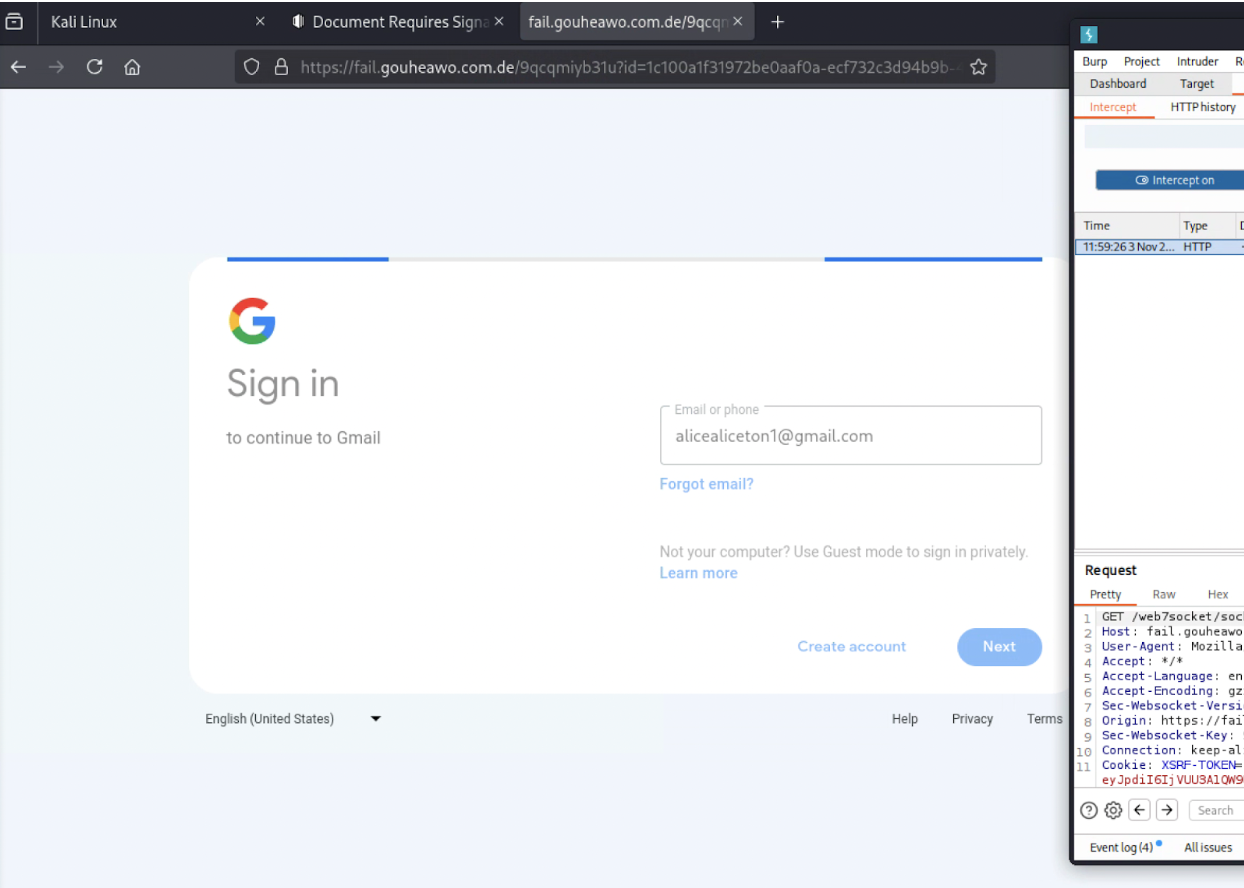
I'm looking over NextDNS as a way to protect non-VPN connected users from phishing attacks, but I'm disappointed that our latest phishing attack wasn't blocked, even with AI enabled.
Now a few days later, it is still not blocked, but 9.9.9.9 is blocking it.
% nslookup fail.gouheawo.com.de 9.9.9.9
Server: 9.9.9.9
Address: 9.9.9.9#53
** server can't find fail.gouheawo.com.de: NXDOMAIN
% nslookup fail.gouheawo.com.de 45.90.28.78
Server: 45.90.28.78
Address: 45.90.28.78#53
Non-authoritative answer:
Name: fail.gouheawo.com.de
Address: 172.64.80.1Is this a fluke? Is there a way to improve it?
9 replies
-
% nslookup fail.gouheawo.com.de 45.90.28.78 Server: 45.90.28.78 Address: 45.90.28.78#53 Non-authoritative answer: Name: fail.gouheawo.com.de Address: 172.64.80.1 % nslookup fail.gouheawo.com.de 1.1.1.1 Server: 1.1.1.1 Address: 1.1.1.1#53 Non-authoritative answer: Name: fail.gouheawo.com.de Address: 172.64.80.1 ~ % nslookup fail.gouheawo.com.de 1.1.1.2 Server: 1.1.1.2 Address: 1.1.1.2#53 Non-authoritative answer: Name: fail.gouheawo.com.de Address: 0.0.0.0It looks like cloudflare 1.1.1.2 is also blocking now. I can see the detection on https://otx.alienvault.com/indicator/hostname/fail.gouheawo.com.de
Can I report this to nextdns? where are the sources from?
-
Heyo,
Looks like only 3 av's class it as a not so good site.... maybe it's a false positive on your side?
https://www.virustotal.com/gui/url/94aa3703727f18dfc3f05959308953bedc87b36211133ba9b75b166d30207c47 -
A new one came up, very similar phish, the phising attack involves the IOCs:
siohoosou.trafrukai.com[.]ru
tnwbrazil.com[.]br/rr/az/
the Russian site only generated the Gmail login after I logged in to a test account (setting Gmail cookies) and set my user agent to Windows/Chrome. (I'm guessing the user-agent was the real reason it started to work.)
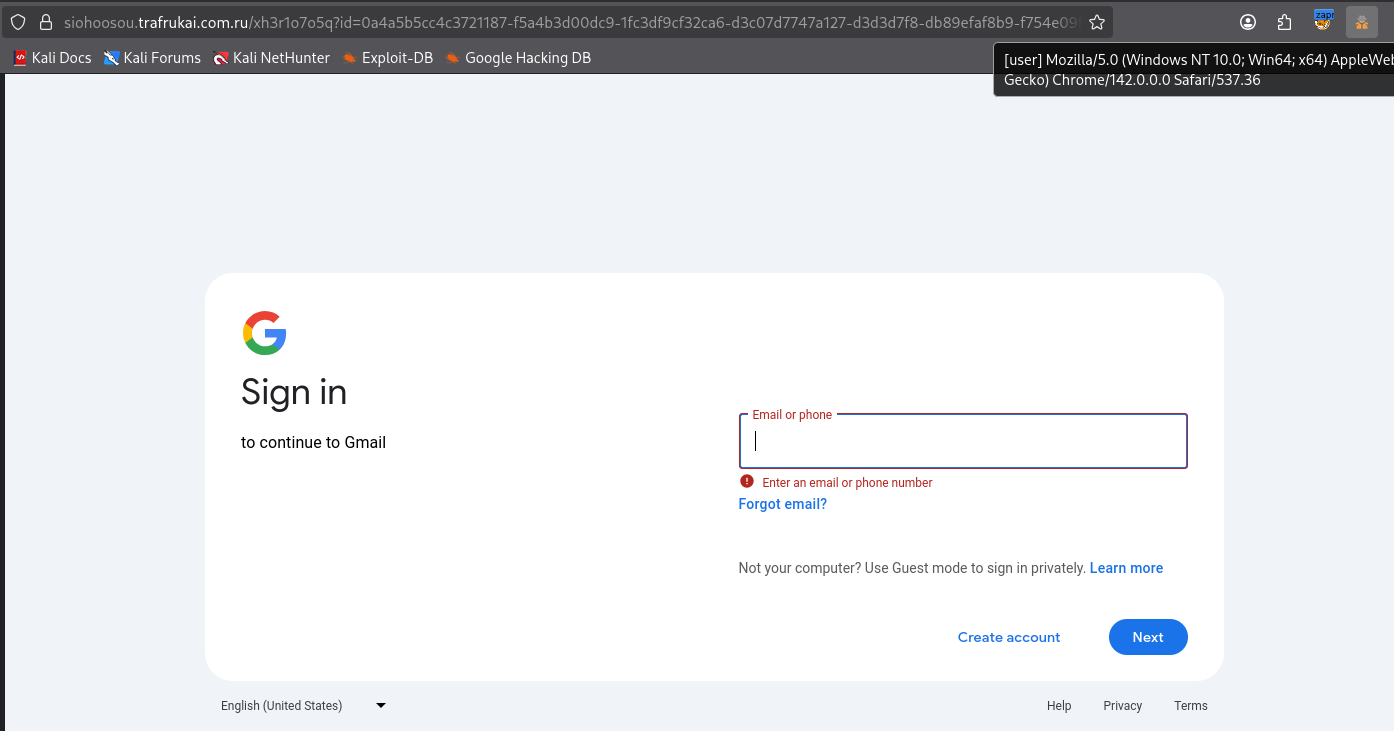
It appears to be hosted on Cloudflare again.
I turned on the AI and while it blocks the old German site, the new Russian one is not detected.
This time though nobody's blocking it, not Cloudflare, Quadnine or NextDNS
Content aside
- 5 mths agoLast active
- 9Replies
- 251Views
-
2
Following